The Onion Router or Tor, as it is commonly known, provides the users with a method to browse and surf the web anonymously. The Tor network makes it difficult for people to have an access to your online data or internet traffic to and fro from your device. You can understand more about the functioning of the Tor below.
Browsing the Deep Web
The internet you can access today comprises of over a billion different websites. But this part of the web only forms about 4% of the actual World Wide Web. The remaining 96% of the web is inaccessible to people as these websites are not indexed. This part of the web is known as the deep web and is full of hidden government secrets, scientific reports, legal documents and more. However, you cannot access the deep web sites and darknet markets without the Tor Browser.
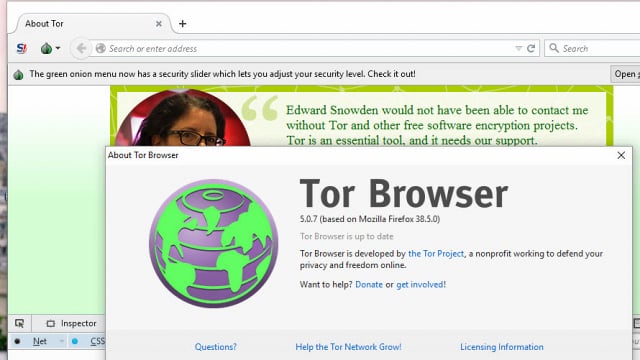
You can download the Tor Browser bundle from the internet depending upon your system requirements and follow the startup guide to know more about how Tor Browser works. Besides helping you access the deep web, the Tor also ensures that your identity is always protected online.
Browsing the Dark Web
A sinister, scarier part of the Deep web hidden well below the surface web is theDark web. This area of the internet is full of illegal activities and criminal dealings. You can find a number of murderers, paid assassins, killers, drug and weapon dealers and match fixers here. While you are browsing the dark web, it is important to know that taking part in these activities is illegal and if caught, you could be in big trouble.
It is very important to take a number of steps to ensure your safety on the deep and dark web. Tor browser helps to protect you against most of these threats by making you anonymous on the web. Additionally, you can use VPN services to protect you online. All the sites running on the dark web use the Tor encryption tool to hide their original identity.
How does the TorBrowser function?
The whole Tor network is spread across the whole world with a number of volunteers running computer servers on their end to provide you with a remote location IP Address. The data you send on the web enters the Tor network in the form of an encrypted packet. The packet’s header is stripped by the Tor to protect the sender’s identity and it encrypts the remaining address information to route the data packet to the final destination via a number of servers or relays.
These relays have the capability to decrypt enough information to understand from which server the data arrived and where it has to be sent next. Doing this ensures that it would be difficult to fully trace the data packet’s path on the Tor network.
How to use theTor Browser?
To use the Tor Browser on your device, you would have to download the appropriate bundle first. Once download you can extract the files to a folder on your device.
- Open the folder to “Start Tor Browser.exe” file.
- The file will prompt you to directly connect to the Tor Network or ask you if you want to make any changes to the proxy settings.
- For basic users, the pre-configured settings are good enough to keep them protected on the internet. Hence, they can directly choose the “Connect” option.
- The Tor browser will now try to initiate a connection with the network and once it is fully established, you will be able to see a version of Firefox on your device. You can safely browse the deep web and the dark web now.
One thing that you must keep in your mind is that, despite being anonymous on the internet, you are still vulnerable to viruses and malware. This is why it is advisable to not browse on unverified websites on the deep web or try to install any software from the deep web. You need to exercise caution on the deep web otherwise you will be vulnerable to being observed by online spies and hackers.
The Last Words
The Tor Browser has become one of the most important tools for web surfers because it is able to protect their identity online and keep them anonymous. Additionally, you can easily access any website which is region-locked without having to bypass it through any illegal methods. While the Tor Browser is not fully fool-proof, the degree of anonymity on the network is very high. However, you can still be traced. Therefore, it is important to know that while surfing on the Tor browser through the deep and dark web, do not indulge yourself in illegal activities. Getting caught taking part in such activities by anyone can put you in a lot of trouble.